📰 ABA TECHSHOW 2026 Recap: From AI Hype to LLM Reality, Google Workspace, and Ethical Lawyering in the Age of Bots ⚖️🤖
/The Real Story Behind ABA TECHSHOW 2026
The techshow is the conference to go to keep your pulse on the technology lawyers should be using every day!
Walking into ABA TECHSHOW 2026 this year, I wasn’t thinking about shiny gadgets; I was thinking about competence, client service, and what it will mean to practice law in an era dominated not just by “AI,” but by large language models (LLMs) quietly shaping almost everything we see and share online. During my work on The Tech-Savvy Lawyer.Page blog and podcast, I keep running into the same pattern: lawyers know they should understand legal technology, yet they worry they’ll break something, breach a rule, or look foolish in front of their staff. TECHSHOW 2026 aimed directly at that anxiety — but this year, the conversation needs to go beyond what AI and generative AI can do and toward how LLMs and search bots are already shaping our professional identities online and offline. ⚖️💻
Keynotes: The “AI Dividend” and Your Time
The keynote lineup captured the tension between promise and risk. Legal market analysts highlighted what some called the “AI Dividend”: when machines take over routine drafting and research, lawyers gain time to think, advise, and advocate at a higher level. The real question — one I’ve been hammering on The Tech-Savvy Lawyer.Page for years — is what you will do with the time technology gives back (some of that time should include reviewing your work, e.g., your case citations). Tech-savvy speakers pushed attendees to look past vendor hype and focus on the broader digital environment, where consumer-facing tools, search engines, and recommendation algorithms are setting new expectations for speed, transparency, and availability.
Practical AI in the Sessions
Inside the conference rooms, the “Taming the Machines” and related AI tracks met baseline concerns (some with hands-on workshops) focused on realistic use cases: assisted drafting, pattern spotting in discovery, and summarizing voluminous documents. These sessions were built for lawyers who live in Word, Outlook, Google Workspace, and practice management systems and who simply want to stop retyping the same paragraphs. The faculty hammered home a critical point: generative AI is an assistant, not a decision-maker; you remain the lawyer, responsible for accuracy, judgment, and ethics under the ABA Model Rules. 🤖📄
Google Workspace, Microsoft 365, and Using What You Already Own
Mathew Krebis’ session on Google Workspace drove that message home in very practical terms. He showed how many firms are only scratching the surface of tools they already pay for: shared Drives with well-structured permissions, real-time collaboration in Google Docs, Gmail automation for intake and follow-up, and Google Calendar combined with Tasks to keep matter timelines under control. When you layer in emerging AI features in Workspace — smart replies, document summaries, suggested outlines — you see how even modest use of these tools can dramatically reduce friction in daily practice, and the tools Mathew discussed are not isolated to “law practice management” systems.
The takeaway was powerful: before you chase a new platform, fully exploit the ecosystem you already have. For many firms, “being more tech-savvy” starts with properly configuring their Google Workspace, Microsoft 365, or other SaaS platform, rather than buying yet another service.
Podcasting, Social Media, and LLM-Driven Visibility
Meanwhile, one other yet important frontier — and one that still feels underexplored — is what happens when LLMs and search bots become the primary lens through which clients, colleagues, and even opposing counsel discover you. That’s where my panel, 🎧 Podcasting for Lawyers: The Truth Behind the Mic, came in.
Ruby L. Powers, Gyi Tsakalakis, Stephanie Everett, and I discussed podcasting and social media not just as marketing channels, but as structured signals fed into LLM-driven engines that are constantly indexing, ranking, and inferring who is an authority on a given topic. Whether you talk about appellate practice, family law, or even a hobby outside the law, your content becomes training data for Generative Engine Optimization/LLM bots that decide which voices surface first when someone types a question into an AI chatbox. 🎙️🌐
In other words, your digital footprint is no longer static. It is being interpreted, reassembled, and presented as answers — often without you ever seeing the intermediate steps. That reality raises a new layer of ethical questions under the ABA Model Rules. Model Rule 7.1’s prohibition on false or misleading communications about the lawyer or the lawyer’s services takes on a new twist when LLMs remix snippets of your posts, podcasts, Google Workspace–hosted client alerts, and blog articles into composite “advice.”
You might be scrupulously accurate in your content, but if an LLM mischaracterizes it or presents it out of context, what then? TECHSHOW 2026 addressed traditional risks like hallucinated case citations, but there is room for a deeper, explicit conversation about how LLM-driven discovery intersects with advertising, communication, and competence duties.
EXPO Hall: Tools, Timekeeping, and Vendor Reality Checks
The EXPO Hall, as always, served as a laboratory of possibilities. Practice management platforms, billing tools, document automation, and a wave of AI-enhanced products competed for attention. Timekeeping tools that automatically capture activity across devices and applications and then propose draft time entries have grown dramatically since last year. For lawyers still reconstructing their days from memory and sticky notes, this is more than a marginal upgrade; it directly affects revenue, work-life balance, and accuracy.
But the fair warning comes here: make sure vendors are showing you what their product can do today, not what they hope it will do someday. In the LLM era, marketing decks are often several steps ahead of deployed reality. 🧾⏱️
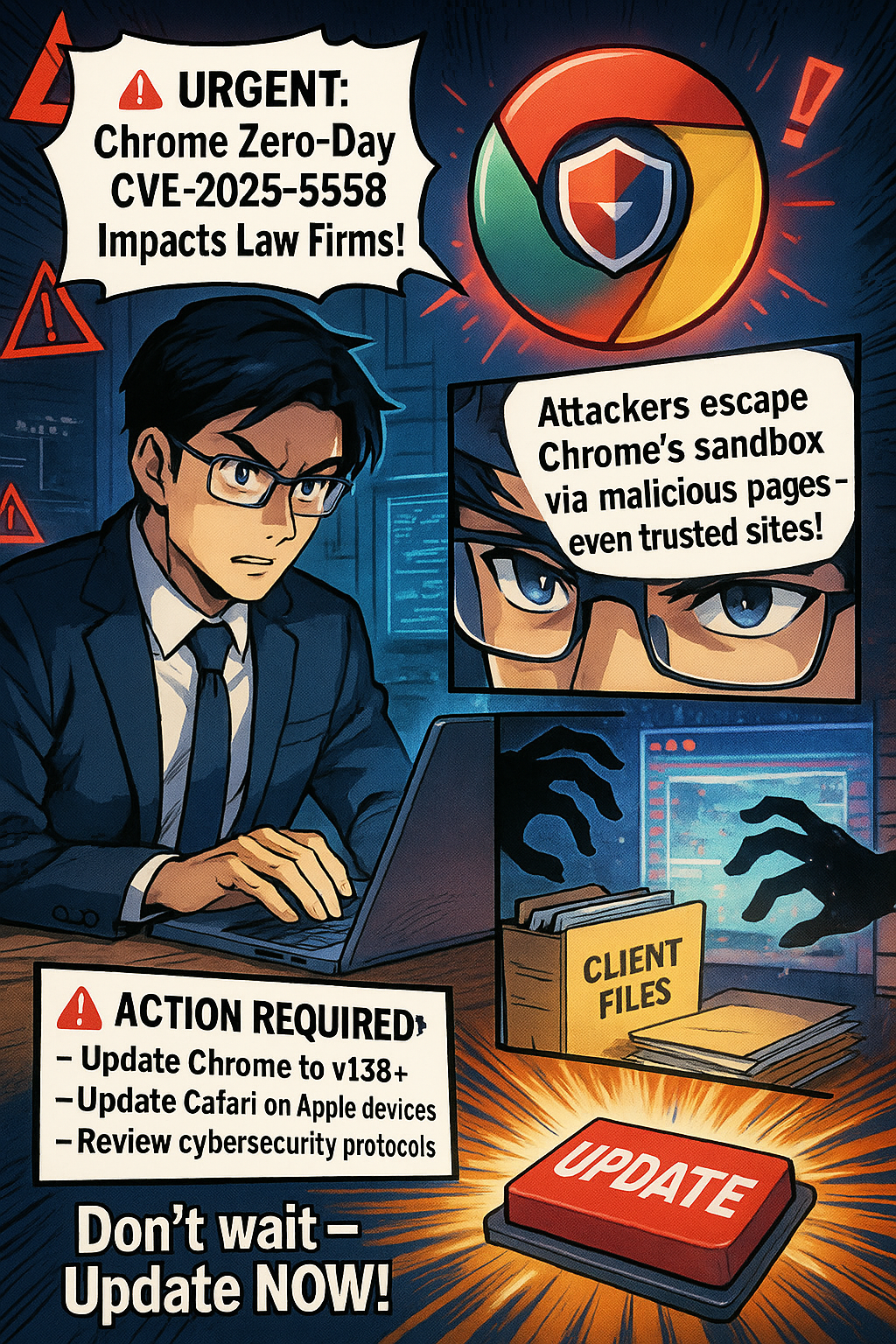
Remember, you have an obligation under Model Rule 1.1 (competence) and Model Rule 5.3 (responsibilities regarding non-lawyer assistance) to understand the capabilities and limitations of any tech you “delegate” work to. Asking hard questions about current functionality, data handling, and audit trails is not being difficult; it is part of your duty of care.
Cybersecurity, Confidentiality, and LLM Risk
networking oppOrtunities like the taste of tecHshow” is a great way to talk with and learn from other lawyers about using tech in the practice of law.
The sessions on cybersecurity and confidentiality continued to do vital work. Under Model Rule 1.6, our obligation to protect client information extends to cloud storage, email, video conferencing, and the mobile devices we casually use in airport lounges. The “Guardians of the Data” track walked through practical checklists rather than abstract fearmongering: password managers, multi-factor authentication, properly configured backups, and vendor due diligence.
For firms running on Google Workspace, that translated into concrete steps: enforcing two-step verification, tightening Drive sharing settings, using client-specific shared Drives instead of ad hoc personal folders, and monitoring admin logs for suspicious access. The move from generic “AI” to LLM-powered services on any platform increases data risk, because many tools rely on ingesting your content — sometimes including client information — to improve their models. If you don’t understand where your data is going and how it is used, you cannot credibly say you are meeting confidentiality obligations. 🔐☁️
Competence, Human-in-the-Loop, and Everyday Workflows
You have an obligation under Model Rule 1.1 (competence) and Model Rule 5.3 (responsibilities regarding non-lawyer assistance) to understand the capabilities and limitations of any tech you “delegate” work to. Asking hard questions about current functionality, data handling, and audit trails is part of your duty of care.
Balancing this skepticism, though, is an equally important truth: becoming proficient with AI and LLM-based tools is not a spectator sport. You cannot satisfy your duty of technological competence from the sidelines. You have to use the tools first on a small scale, then progressively in more critical workflows, always with appropriate supervision and verification.
That might mean piloting an AI drafting feature in Google Docs and Microsoft Word for internal templates, or testing structured intake forms and automations inside Google Workspace or Microsoft 365 before rolling them out firm-wide. Ignoring AI because it feels uncomfortable is no longer the safer option. In some practices, failing to integrate it intelligently — while peers and opposing counsel do — may itself raise competence concerns as expectations evolve in courts and among clients. 🧩📈
Saturday Sessions: From “Use AI” to “Use AI Responsibly”
On Saturday, the 9 a.m. conversation among ABA President Michelle A. Behnke, Immediate Past President William R. “Bill” Bay, and President-Elect Barbara J. Howard, underscored how all of this ties into the rule of law and access to justice, framing AI as something lawyers now have a responsibility to actually use, not simply watch from the sidelines. The 10 a.m. session with Judge Timothy S. Driscoll then shifted the focus from “use AI or be left behind” to “use AI responsibly,” making it clear that judges, too, are integrating AI into their work and that they are not immune from mistakes when they rely on it.
The message for everyone in the courtroom ecosystem was simple and blunt: “Review, review, and review” any work touched by AI, because AI is a non‑infallible tool that does make errors and can mislead the unwary. Together, these sessions acknowledged the growing digital divide: lawyers and clients who can’t or won’t adopt technology risk falling out of the mainstream of legal services, while those who adopt it recklessly risk eroding confidence in both their own work and the justice system as a whole.
We are not merely debating convenience; we are deciding who gets effective representation and who is left out because the lawyer they might have hired never appeared in their LLM‑driven search results — or appeared with AI‑boosted visibility but poor ethical judgment. Technology, in this sense, is not optional; it is one of the few levers we have to expand meaningful access to legal help, provided we wield it with intent, humility, and rigorous human review. ⚖️🧠
LLM Literacy: The Next Core Competency
That balance — between caution and experimentation — is where TECHSHOW 2026 both excelled and showed its next frontier. Many sessions made AI approachable, breaking down concepts for lawyers with limited to moderate tech skills and providing concrete workflows they could apply on Monday. What I would like to see more explicitly next year is programming that treats LLM literacy as a core competency: understanding how LLMs are built, how they index and surface information, how your content feeds into them, and how that affects everything from client intake to reputation, whether you are working in Microsoft 365, Google Workspace, or a specialized legal platform.
From my vantage point as a legal tech ambassador at The Tech-Savvy Lawyer, the most successful sessions respected that many lawyers are highly capable professionals who simply haven’t had the time or guidance to modernize their workflows. They don’t need to become prompt engineers. They need guardrails, roadmaps, and clear examples of how to align AI, LLM tools, and mainstream platforms like Microsoft 365 and Google Workspace with the ABA Model Rules and local bar guidance. When faculty focused on incremental steps — tightening cybersecurity configurations, adding a layer of AI-assisted drafting under strict human review, building a consistent content strategy that LLMs can reliably recognize — the room should lead in.
A Tough-Love Takeaway for Lawyers
If you are a lawyer who still feels behind, here’s the core message I took away from TECHSHOW 2026, with a bit of tough love: you don’t need to chase every new tool, but you can’t afford to ignore LLM-driven AI and the platforms you already live in, like Microsoft 365 and Google Workspace, any longer. Understand the basics; pilot one or two well-vetted tools to start improving your efficiency without sacrificing the need for a true human-in-the-loop.
SEE YOU IN CHICAGO FOR ABA TECHSHOW 2027!!!
Read your jurisdiction’s ethics opinions on AI and technology. Build habits that protect client data by default. Use your own content — whether blog posts, newsletters, or podcasts — to train the bots to see you as a trusted authority rather than a digital afterthought. Ultimately, your bar license may be at more risk from not engaging with AI than from engaging with it carefully and intelligently.
The future of legal practice will not wait until we are all comfortable; it is here now, embedded in the search boxes, recommendation engines, and tools your clients already use. TECHSHOW 2026 made that clear. The next move is yours. 🚀⚖️
MTC